SA urged to pursue cybersecurity frameworks based on global best practice




FATIMA AMEER-MIA Codifying cybercrime definitions and transgressions in a well defined legal framework should be used in conjunction with a digital technology and cybersecurity framework to provide guidance and rules to allow for effective enforcement of cyber-related crimes
BRUCE WATSON Cybersecurity laws must allow for cross-border data flows while requiring suitable protection of the information
NIEL VAN ROOYEN To make headway against cybercrime requires that all stakeholders must collaborate and use best practices and international principles to improve data security and enforce data protection
The data that public and private organisations capture and use, as well as its sensitivity, risk, and protection, are central not only to international cybersecurity best practice, but also to laws and regulation.
Information and communication technology (ICT) and law experts indicate that data, as a valuable asset for organisations and often containing personal and sensitive information, is fundamental to determining the risks, suitable protection and management of data that must be undertaken by organisations.
South Africa’s digital interactions and cybersecurity, notwithstanding the Cybercrimes Bill 2017 that has not yet been adopted, are currently governed by the Electronic Communications and Transactions Act (ECTA No 25 of 2002), as well as the Protection of Personal Information Act (Popi Act No 4 of 2013), says law firm Cliffe Dekker Hofmeyr (CDH) technology, media and telecommunications practice director Preeta Bhagattjee.
While civil and criminal charges for cybercrimes can be laid against people or organisations under Section 87 of the ECTA and under a range of criminal laws, there is still a significant amount of work required to bring South African legislation in line with international principles and standards, including defining various cybersecurity concepts within a legal framework, which the Cybercrimes Bill partly aims to address, she adds.
“Without a well defined legal framework, it is more difficult, but not impossible, to prosecute people or organisations implicated in cyberattacks and crimes, which weakens enforcement. Data protection legislation often goes hand in hand with cybersecurity laws.”
The Popi Act is in force – although enforcement provisions will come into effect only in July – and provides definitions for important elements, including data breaches, personal information and reasonable protection, which are aligned to international data protection principles, says Bhagattjee.
CDH technology, media and telecommunications practice director Fatima Ameer-Mia adds that it is important to codify the various definitions and transgressions in relation to cybercrime in a well defined legal framework, which, although present in older laws, are often fragmented across various legislation. This, in conjunction with a digital technology and cybersecurity framework, should be used to provide guidance and rules to allow for effective enforcement of cyber-related crimes.
“These broad guidelines are contained in the [Cybercrimes] Bill. Corporate, healthcare and financial institutions, for example, are bound by codes of conduct and industry-specific regulations, and have implemented cybersecurity according to the sensitivity of the data they process and the industries’ potential exposure to criminal activities. The Popi Act, for example, requires that ‘reasonable measures’ be taken to adopt appropriate security safeguards and mitigate the risks of data losses.
“Many of the measures required to protect organisations in different industries are not specifically set out in the legislation, and many organisations thus look to international best practices and industry standards to determine what measures should reasonably be taken,” she says.
All government departments, agencies, State-owned enterprises and institutions are also regulated under South Africa’s data protection laws, and must similarly identify and protect the data that they hold, notes Bhagattjee.
Additionally, while capacity is built up in police organisations to conduct forensic investigations of cybercrimes, private organisations and cybersecurity forensic experts will also be needed to conduct investigations, which will add to the body of evidence in criminal cases.
IBM Security in Southern Africa business unit leader Sheldon Hand emphasises that every country will want to create a cybersecurity team or centre with expertise to respond to national security ICT threats and attacks.
This capacity will be separate from civil and criminal ICT forensic teams, which will be needed as part of police resources to investigate and find evidence of cybercrimes for litigation and prosecution.
“Many attacks [against countries] are carried out against critical infrastructure, usually motivated by financial gain. Governments and public organisations also hold lots of information and often critical information about individuals, which requires protection.”
Attacks on national assets and private individuals and organisations will require private and public cybersecurity skills, which must be collaborated with to combat attacks against States and criminal attacks against private organisations, adds Hand.
Defence Decisions
There are many cybersecurity frameworks, standards and practices that organisations can use to inform their cybersecurity strategy, but the starting point in all cases is to identify the data that they have, says ICT services multinational T-Systems South Africa specialist sales executive Lukas van der Merwe.
The risks and threats to the protection of data can then be determined. Knowing what data is sensitive and how it is used, shared and stored will support subsequent initiatives to detect, contain and mitigate threats and attacks, as well as how to recover it. This is best practice and part of a feedback loop to continuously improve an organisation’s cybersecurity, he adds.
“A risk assessment of an organisation’s data will also inform suitable access controls and access management, and help to identify gaps in protection that can be met using various tools and systems.”
Prioritisation based on risks is necessary because not all data can, nor should, be defended equally; it must be protected in proportion to its sensitivity and to meet regulations, whether local laws or international trade or supply chain requirements, he explains.
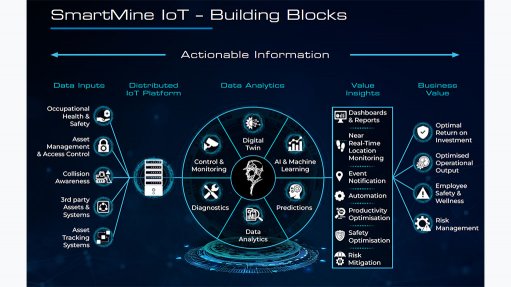
Differences in operating environments, such as in manufacturing, requires that the security of other systems, such as operational technology, Internet of Things and production controls, must also be evaluated for cybersecurity risks and appropriately protected.
“Most of the frameworks have similar and comparable basic steps to support the improvement of cybersecurity in organisations. Industry-specific frameworks and standards provided by companies or industry organisations address industry-specific and operational requirements, and can be used in addition to overarching cybersecurity frameworks.”
The US National Institute of Standards and Technology and the International Organisation for Standardisation publish well-known and widely used international cybersecurity frameworks.
Hand and Van der Merwe separately highlight the work of industry bodies and platforms, such as the South African Banking Risk Information Centre, and their contributions to fostering information exchange and collaboration within industries.
The methods of these platforms and centres can be adopted and adapted to create platforms for various industries and sectors to protect themselves, shore up their defences and improve the integrity of their ICT systems.
Data Stewardship
The Popi Act helped to raise awareness in South Africa of the need to identify and protect data, and prompted companies to implement the necessary controls to protect customer information and personal data, says ICT and network services provider Vox Information Security head Niel van Rooyen.
While this increased awareness is important in catalysing organisations to implement data protection measures, the pressure on cybersecurity defenders is continuously increasing.
“The only way to make headway in the battle against cybercriminals is to collaborate. Industry, governments and cybersecurity organisations must join hands and use best practices, internationally agreed principles and laws to improve data security and regulate and enforce data protection,” he warns.
University of Stellenbosch Information Sciences head of department Professor Bruce Watson adds that cybersecurity legislation must not be myopic by defining rules and transgressions only in terms of national laws.
“Cybersecurity legislation would be wildly unrealistic if it aimed to prohibit data crossing borders. Data are flowing across borders, and it could be difficult – if not impossible – to completely prevent this. Cybersecurity laws must allow for this while requiring suitable protection of the information. Increasingly, there is a need for an international framework for data transmission and stewardship.”
He also emphasises international collaboration, highlighting that cybercrimes are very often cross-border crimes.
“Similar to cross-border criminal pursuit agreements between nation-States, we should have agreements to exchange pertinent information and evidence to combat cyberthreats and attacks and prosecute people involved in cybercrimes.”
Sharing information about cyberthreats and attacks is important to allow for systems to be patched and vulnerabilities closed quickly by sending updates, emphasises Hand.
“Cybercriminals collaborate to share exploits and attack methods. The cybersecurity industry has to collaborate. Cybersecurity information sharing is far more common and better than ten years ago, and there are no insurmountable barriers to further improving data sharing.”
Commercial and industrial organisations do not share information unless identifying information has been removed, but are happy to share information about attack methods and threat intelligence, as long as they share the information with their stakeholders and regulators first, he adds.
Adopt and Adapt
Most large South African companies, multinational enterprise subsidiaries and companies supplying international value chains have been influenced by the laws of countries they operate in or trade with, or by industry requirements and best practices to improve their cybersecurity measures, says Watson.
Most organisations already subscribe to a set of standards for their cybersecurity, and South Africa can use existing and well- developed standards, best practice guidelines and frameworks to shape a localised version, similar to the Popi Act, confirms Hand.
“The existing cybersecurity frameworks, developed by many organisations such as the Cloud Security Alliance that produces its own cloud security framework, allow organisations to benchmark their efforts against international guidelines and standards, and thereby help local organisations adhere to international cybersecurity standards,” he says.
There are no barriers to South Africa adopting and adapting legal and enforcement frameworks from countries that have developed and implemented cybersecurity laws, such as Estonia, which has notable experience in this area, highlights Watson.
Similarly, economic regions, such as the Southern African Development Community, can lean on learnings from other economic regions, such as the European Union, which has grappled with the implementation, policing and enforcement of the General Data Protection Regulation across different jurisdictions.
Many data leaks and breaches are a result of human error or malicious actions. People in any organisation must at least be made aware of their organisation’s cybersecurity strategy and their roles in defending its data and systems, says Van Rooyen.
Hand adds that an incident response strategy and step-by-step process are critical to ensure all the teams and departments know what to do to contain and mitigate a detected breach.
“There is no silver bullet or magic wand to cybersecurity; it is a deliberate, progressive process. The quicker an organisation can respond to a detected attack, the lower the damage and costs to recover from the attack,” he states.
Cybersecurity is an organisational risk, just like any other business process, and requires that organisations and their leaders maintain a suitable cybersecurity posture to sustain the organisations as the world continues towards a new digital era, concludes Van der Merwe.
Article Enquiry
Email Article
Save Article
Feedback
To advertise email advertising@creamermedia.co.za or click here
Press Office
Announcements
What's On
Subscribe to improve your user experience...
Option 1 (equivalent of R125 a month):
Receive a weekly copy of Creamer Media's Engineering News & Mining Weekly magazine
(print copy for those in South Africa and e-magazine for those outside of South Africa)
Receive daily email newsletters
Access to full search results
Access archive of magazine back copies
Access to Projects in Progress
Access to ONE Research Report of your choice in PDF format
Option 2 (equivalent of R375 a month):
All benefits from Option 1
PLUS
Access to Creamer Media's Research Channel Africa for ALL Research Reports, in PDF format, on various industrial and mining sectors
including Electricity; Water; Energy Transition; Hydrogen; Roads, Rail and Ports; Coal; Gold; Platinum; Battery Metals; etc.
Already a subscriber?
Forgotten your password?
Receive weekly copy of Creamer Media's Engineering News & Mining Weekly magazine (print copy for those in South Africa and e-magazine for those outside of South Africa)
➕
Recieve daily email newsletters
➕
Access to full search results
➕
Access archive of magazine back copies
➕
Access to Projects in Progress
➕
Access to ONE Research Report of your choice in PDF format
RESEARCH CHANNEL AFRICA
R4500 (equivalent of R375 a month)
SUBSCRIBEAll benefits from Option 1
➕
Access to Creamer Media's Research Channel Africa for ALL Research Reports on various industrial and mining sectors, in PDF format, including on:
Electricity
➕
Water
➕
Energy Transition
➕
Hydrogen
➕
Roads, Rail and Ports
➕
Coal
➕
Gold
➕
Platinum
➕
Battery Metals
➕
etc.
Receive all benefits from Option 1 or Option 2 delivered to numerous people at your company
➕
Multiple User names and Passwords for simultaneous log-ins
➕
Intranet integration access to all in your organisation